CCTV Footage- Primary Evidence-
CCTV footage directly & immediately stored in hard drive of computer is original media, self generated & created without human intervention- Not secondary evidence & does not require certification u/s 65B of Evidence Act. Kishan Tripathi v. State, Crl.A.108/13, 12.2.16 DHC
-—-–—–-—––—-–—
: Procedure to be followed by Magistrate when CCTV footage and video recordings is produced by police at the time of filing of chargesheet?
During the hearing of the case, we noticed that the trial Court had not played the DVR (MO-2) and seen the CCTV footages in the presence of the accused. In this regard we propose to dispel misgivings, if any, in the mind of trial Judges about their power to view such evidences. There will be instances where, by the time the case comes up for trial in one court, the electronic record would have had a natural death for want of proper storage facilities in the Court property room. To obviate these difficulties, we direct that, on a petition filed by the prosecution, the Judicial Magistrate, who receives the electronic record, may himself view it and take a back up, without disturbing the integrity of the source, in a CD or Pendrive or any other gadget, by drawing proceedings. The back up can be kept in safe custody by wrapping it in anti static cover and should be sent to the Sessions Court at the time of committal. The present generation of Magistrates are computer savvy and they only require legal sanction for taking a back up. They can avail the service of an expert to assist them in their endeavour. Recently the Supreme Court in Shamsher Singh Verma v. State of Haryana, MANU/SC/1345/2015 : 2015 (12) Scale 597, has held that CD is a 'document' within the meaning of Section 3 of the Indian Evidence Act, 1872. In Ziyauddin Burhanuddin Bukhari v. Brijmohan Ramdass Mehra, MANU/SC/0277/1975 : (1976) 2 SCC 17, the Supreme Court has held that tape records of speeches are 'documents' as defined in Section 3 of the Indian Evidence Act, 1872. This Judgment has been relied upon in Shamsher Singh Verma's case (cited supra). Therefore, we hold that articles like Memory Card, Hard Disc, CD, Pen-drive, etc., containing relevant data in electronic form are 'documents' as defined under Section 3 of the Indian Evidence Act, 1872, albeit, marking them as material objects. After all, nomenclature cannot have the effect of altering the characteristics of an object. The words 'proved' and 'disproved' in section 3 of the Evidence Act have the following common denominator;
"A fact is said to be proved/disproved when, after considering the matters before it............ "
(emphasis supplied)
Without viewing the CCTV footage, how can any Court, "consider the matter before it " to conclude that a fact has been 'proved' or 'disproved' ? That apart, Section 62 of the Indian Evidence Act, 1872 states,
"Primary evidence means the document itself produced for the inspection of the Court."
(emphasis supplied).
This does not mean that, if a secondary evidence of a document is admitted lawfully, the Court is denuded of the power to inspect it. Such an inference will lead to absurdity. Therefore, we hold that a Court has the power to view CCTV footage and video recordings, be it primary or legally admissible secondary evidence, in the presence of the accused for satisfying itself as to whether the individual seen in the footage is the accused in the dock. The trial Court should also specifically put questions to the accused when he is examined under Section 313 Cr.P.C. about his overt acts appearing in the footage and record his answers.
IN THE HIGH COURT OF JUDICATURE AT MADRAS
Dated: 27.2.2016.
: IN THE HIGH COURT OF JUDICATURE AT MADRAS
Dated: 27-1-2016
Coram
The Honourable Mr.Justice R.SUDHAKAR and
The Honourable Mr.Justice P.N.PRAKASH
Referred Trial No.1 of 2015
Criminal Appeal No.110 of 2015
K. Ramajayam @ Appu Appellant/Accused
Vs.
The Inspector of Police,
-—–—-—–—–—
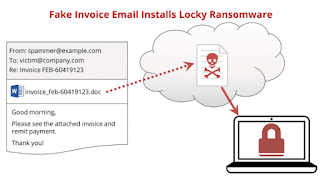
SC: Computer Output not admissible without Compliance of 65B,EA
In the judgment of ANVAR P.V. VERSUS, P.K. BASHEER AND OTHERS, in CIVIL APPEAL NO. 4226 OF 2012 decided on Sept., 18, 2014, the Supreme Court has settled the controversies arising from the various conflicting judgments as well as the practices being followed in the various High Courts and the Trial Court as to the admissibility of the Electronic Evidences. The court has interpreted the Section 22A, 45A, 59, 65A & 65B of the Evidence Act and held that data in CD/DVD/Pen Drive are not admissible without a certificate u/s 65 B(4) of Evidence Act. It has been clarified that in case of computer output without such a certificate, neither there cannot be oral evidence to prove such a electronic evidence the output in electronic media nor the opinion of the expert under section 45A Evidence Act could be resorted to prove the genuineness
-—–-–—-–—
Fact discovered - what constitutes - Fact means some concrete or material fact to which information directly relates - Information must be such as has caused discovery of the fact & must relate distinctly to the fact discovered -
2010 ALL SCR (OCC) 146 -
Erabhadrappa V/s. State of Karnataka
------------------------------------------------
Electronic Evidence Case Law: CCTV & 65B Certificate
Rajesh Dhannalal Daware Vs. State of Maharashtra {Bombay High Court, 5 May 2016}
Evidence Act, 1872 - Section 65-B - Footage of CCTV Camera - Under S. 65B(4) if it is desired to give a statement in any proceedings pertaining to an electronic record, it is permissible provided the following conditions are satisfied: (a) There must be a certificate which identifies the electronic record containing the statement; (b) The certificate must describe the manner in which the electronic record was produced; (c) The certificate must furnish the particulars of the device involved in the production of that record; (d) The certificate must deal with the applicable conditions mentioned under Section 65B(2) of the Evidence Act; and (e) The certificate must be signed by a person occupying a responsible official position in relation to the operation of the relevant device.